Think proactive IT has zero to little implications for your everyday life? Consider this: Sixteen thousand. […]
You’ve taken a long, hard look at your business and one thing has become very clear: […]
When you hire a company for outsourced IT management, it might be one of the most […]
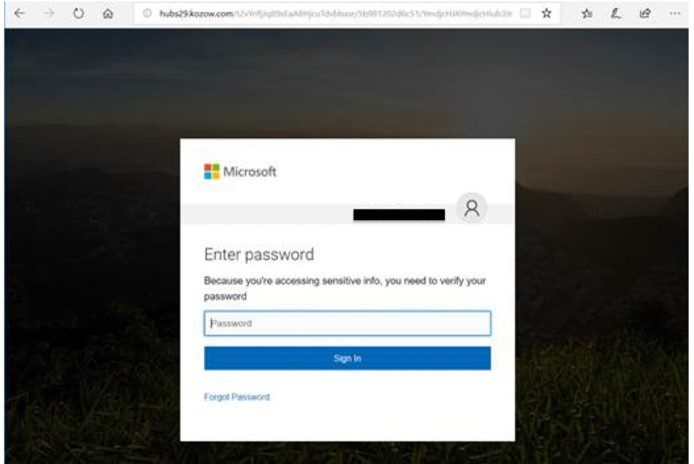
The ever threat of viruses, hacking, and security threats are evolving everyday. So many people think […]
Welcome to SandStorm IT’s 6-part series about Payment Card Industry Data Security Standard (PCI DSS). In […]
A browser cookie is data sent from a website that will be stored on your computer. […]