In today’s digital landscape, operational disruptions can arise from unexpected sources, highlighting the need for robust […]
In the ever-evolving landscape of cybersecurity, recent breaches have underscored the need for robust defenses and […]
Browser cookies are small data files sent from websites and stored on your computer. They play […]
Facebook, like Google, is a website with many interesting and relevant features that a large portion […]
What is Incognito Mode? Incognito mode is essentially a setting on your web browser to disallow […]
A Managed Antivirus service is an automated service that will ensure your antivirus is up-to-date, runs […]
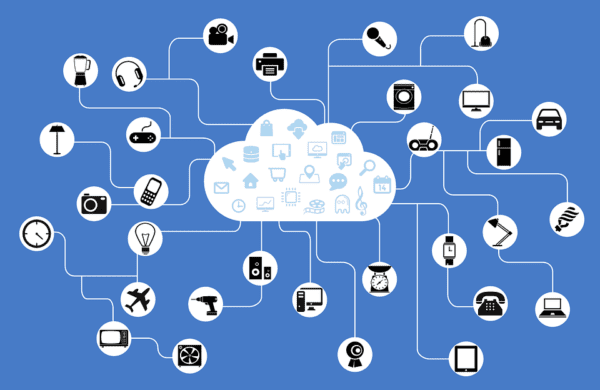
Welcome to SandStorm IT’s 6-part series about the Internet of Things. In this series, we’ll shed […]