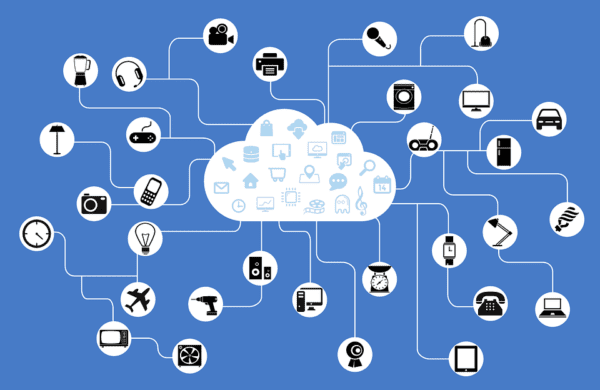
Welcome to SandStorm IT’s 6-part series about the Internet of Things. In this series, we’ll shed some light on the basics of IoT.
Part 1 – What is the Internet of Things (IoT)?
Part 2 – Why do I care about IoT?
Part 3 – What are some real-world applications of IoT?
Part 4 – What are the security concerns of IoT? (You are here)
Part 5 – What devices do I have that connects to IoT?
Part 6 – What is the future of IoT?
In this post, we’ll go over the security concerns of IoT devices. Given their diverse nature, there are many security concerns with IoT products. From self-driving vehicles to smart energy grids (and even kitchen appliances), each device presents its own unique set of consequences when attackers discover vulnerabilities in these systems. Traditionally, gaining illegitimate access to computer systems meant the ability to deface a website or steal data from the victim’s servers. Exploiting security holes in IoT devices can result in the physical destruction of systems, or in the most extreme cases, loss of human life (like in the case of hacking a pacemaker). One major issue with quantifying the impact of IoT device exploits is that these devices’ capabilities are much more varied than a traditional computer’s functionality.
How Secure are IoT Devices?
The security of an IoT device largely depends on the maker of the product and how much time the company invested in securing their products. There is not a one-size-fits-all solution for IoT security because many of them use communication protocols that are tailored to suit their own operations. Prioritizing sales figures over security is an unfortunate reality in many businesses. This can lead to rushed product development, particularly in the realm of security, since general functionality is much more apparent and pleasing to the end user. Although it is hard to gauge individual IoT devices’ security levels, the security of a device will generally greatly improve as updated firmware is available.
How Can I Secure My IoT Devices?
Due to many IoT devices running on custom protocols, one of the most important things you can do before buying an IoT device is to make sure that the product receives updates as necessary. There are bound to be many security vulnerabilities in IoT products that are fresh on the market, and it is imperative that you buy from a company that takes security seriously. Secondly, change any default username and password that comes with the device. Attackers have been known to gain access to many systems simply by looking up a product’s default username and password and plugging those credentials in. Also, as is the case with general password best practices, do not reuse passwords, use a minimum of around 8 characters, and include a capital letter and symbol. If it is not too inconvenient, taking the product off the network when not in use will eliminate potential remote access by attackers.
In our next installment in our Internet of Things (IoT) Series, we’ll cover “What devices do I have that connects to IoT?”.