So everyone’s seen the HTTP and HTTPS prefixes on their favorite website addresses but did you […]
If you’ve ever shopped online for something, you’ve likely come across a special type of ads […]
When does your business need a server? It may not, at least not in the traditional […]
Do you ever wonder “How is this website built?” or “What software is this site running […]
Two Factor Authentication, commonly abbreviated 2FA, is a second layer of authentication in addition to your […]
When decisions are being made about who is managing their network, there is sometimes debate whether […]
A business computer network can be identified as either a workgroup or domain network. There are […]
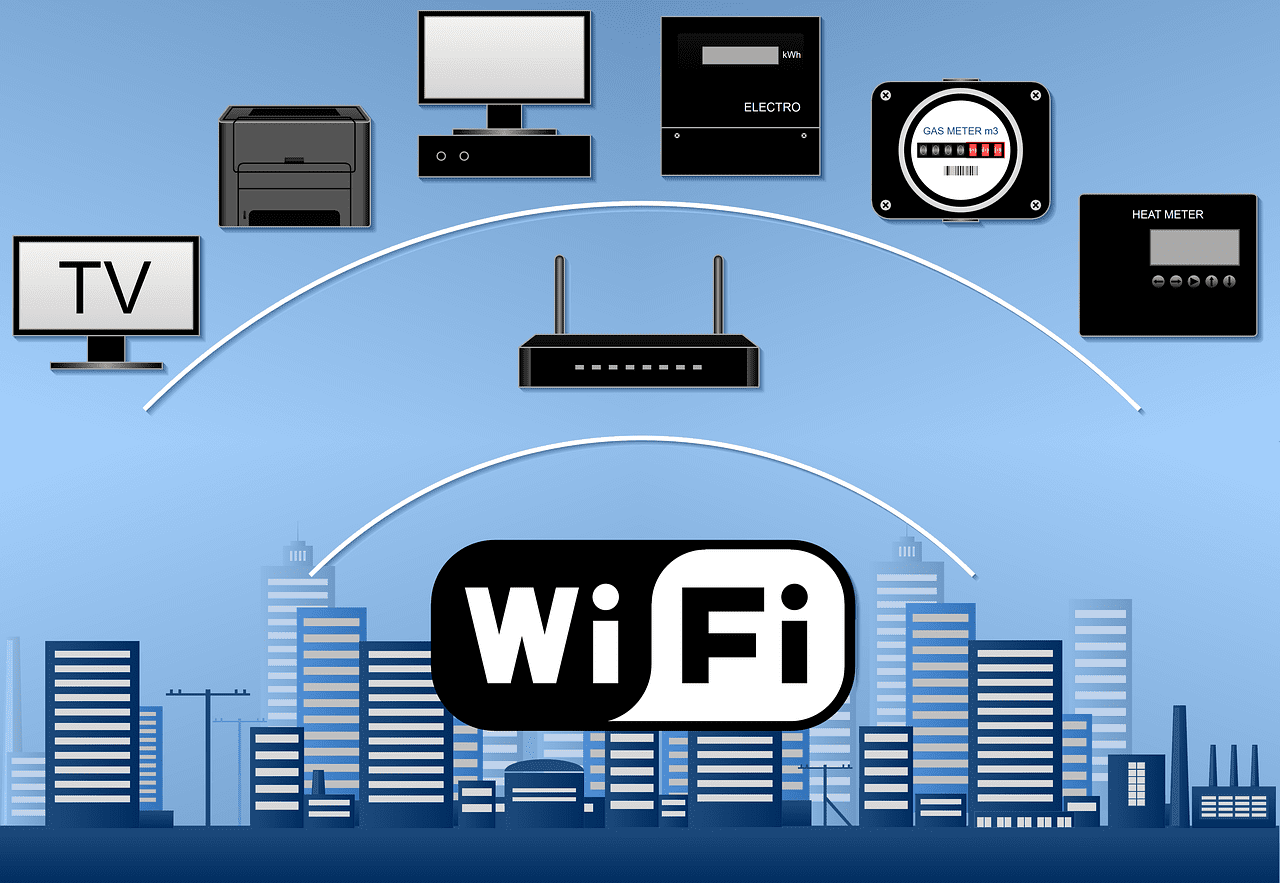
Business Wi-Fi isn’t as simple as setting up a basic home wireless network. How your Wi-Fi […]
As we’ve spoken with current customers and new prospects about Managed IT Services for their computers, […]
You probably can recall the recent story of when Mark Zuckerberg had to testify before Congress […]