Even with the added layer of security of Two-Factor Authentication (2FA), cybercriminals are still finding ways […]
If you’ve used a computer anytime over the past 20 years, you’ve probably been infected by […]
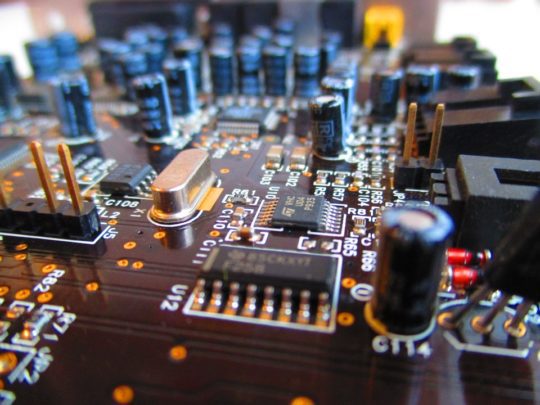
Hardware monitoring is a feature of the motherboard, sometimes as a separate chip on the motherboard, […]
Data Hashing. Encryption. These are words that one hears all the time about the topic of […]