Posts
Latest Posts from Our Blog
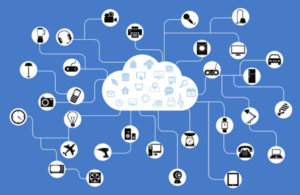
Welcome to SandStorm IT’s 6-part series about the Internet of Things. In this series, we’ll shed some light on the basics of IoT. Part 1 – What is the Internet of Things (IoT)? Part 2 – Why do I care about IoT? Part 3 – What are some real-world applications of IoT? Part 4 – What…
Read MoreIn today’s digital landscape, email communication remains a cornerstone of business operations and personal correspondence. However, with the rise of cyber threats and phishing attacks, ensuring the security and authenticity of emails has become paramount. Two essential tools in this endeavor are DKIM (DomainKeys Identified Mail) and DMARC (Domain-based Message Authentication, Reporting, and Conformance). In…
Read MoreToday, we’re delving into the boundless universe of cloud storage with none other than Microsoft OneDrive. If you’re scratching your head wondering, “What exactly is OneDrive, and how can it elevate my digital life?” fear not! We’re about to embark on a journey to demystify this handy tool and unleash its full potential. What is…
Read MoreWhat would you do if your data was gone, without any kind of warning? How would that impact your life or work? Catastrophes happen in life, often unexpected and uncontrollable. The loss of personal or business data could definitely be considered a catastrophe for most people. Natural Disasters The recent tornados that swept through our…
Read MoreWhat is HIPAA? HIPAA is the Health Insurance Portability and Accountability Act of 1996 that was enacted by Congress and signed into law in 1996. There are many provisions to HIPAA covering many items mostly dealing with health insurance and regulations on what can be offered and how. Additionally, HIPAA also details regulations about a…
Read MoreWe’ve previously covered “What is a Firewall and Why do I Need One?”. In this blog post, we will take a deeper look to see how a Next Generation Firewall (NGFW) can help protect your business. NGFW’s contain all the tried and true features of the firewalls before them but they also contain advanced functionalities.…
Read MoreIn an era where technology seamlessly intertwines with healthcare, ensuring the security and reliability of digital systems is paramount. However, recent events have shaken the foundation of this symbiotic relationship. Change Healthcare, a prominent U.S. health tech company, found itself at the center of a storm as a series of cyber attacks disrupted operations in…
Read MoreAccounting for more than $12 billion in total business losses, the costs of cybersecurity breaches are impacting businesses’ bottom lines more often than ever. The cost of a single data breach averages $149K. With a price tag like that, it’s no surprise that some businesses close their doors after an attack, unable to recover from…
Read More